A stability flaw in the way Microsoft Windows guards people against destructive data files was actively exploited in malware attacks for two decades just before very last week, when Microsoft lastly issued a application update to suitable the difficulty.
1 of the 120 safety holes Microsoft fixed on Aug. 11’s Patch Tuesday was CVE-2020-1464, a issue with the way every supported version of Windows validates digital signatures for laptop applications.
Code signing is the system of using a certification-dependent electronic signature to signal executable files and scripts in buy to validate the author’s identification and guarantee that the code has not been adjusted or corrupted considering that it was signed by the writer.
Microsoft mentioned an attacker could use this “spoofing vulnerability” to bypass security attributes intended to avoid improperly signed data files from being loaded. Microsoft’s advisory would make no mention of security scientists getting advised the corporation about the flaw, which Microsoft acknowledged was actively getting exploited.
In simple fact, CVE-2020-1464 was initial noticed in attacks utilized in the wild back again in August 2018. And many researchers informed Microsoft about the weak spot in excess of the earlier 18 months.
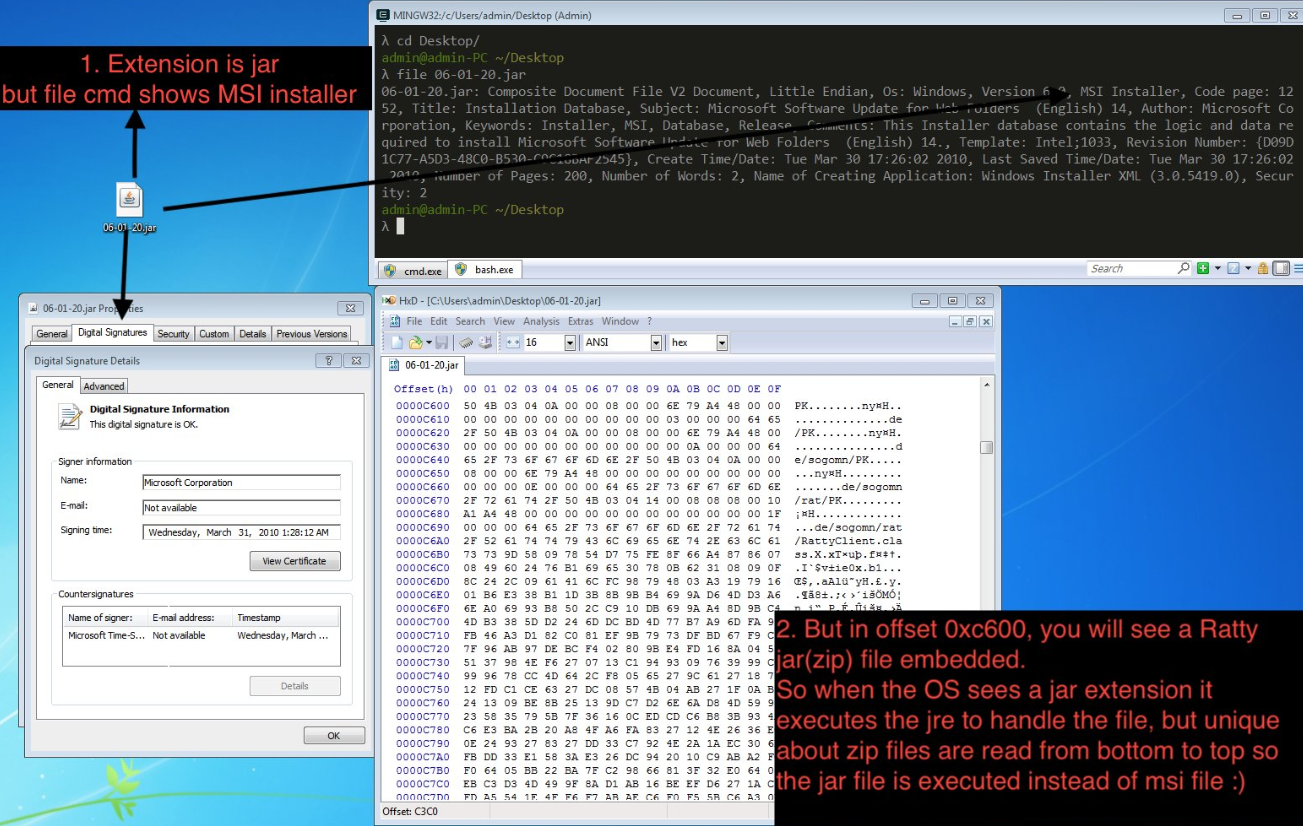
Bernardo Quintero is the supervisor at VirusTotal, a service owned by Google that scans any submitted data files from dozens of antivirus products and services and displays the success. On Jan. 15, 2019, Quintero published a blog site submit outlining how Windows retains the Authenticode signature valid following appending any information to the close of Windows Installer information (those people ending in .MSI) signed by any program developer.
Quintero reported this weakness would specifically acute if an attacker were being to use it to hide a destructive Java file (.jar). And, he said, this actual assault vector was certainly detected in a malware sample sent to VirusTotal.
“In shorter, an attacker can append a destructive JAR to a MSI file signed by a trustworthy software package developer (like Microsoft Company, Google Inc. or any other effectively-acknowledged developer), and the resulting file can be renamed with the .jar extension and will have a legitimate signature in accordance Microsoft Windows,” Quintero wrote.
But according to Quintero, though Microsoft’s safety crew validated his conclusions, the enterprise chose not to deal with the challenge at the time.
“Microsoft has made a decision that it will not be repairing this difficulty in the present versions of Windows and agreed we are ready to website about this circumstance and our conclusions publicly,” his blog site write-up concluded.
Tal Be’ery, founder of Zengo, and Peleg Hadar, senior safety researcher at SafeBreach Labs, penned a weblog put up on Sunday that pointed to a file uploaded to VirusTotal in August 2018 that abused the spoofing weakness, which has been dubbed GlueBall. The very last time that August 2018 file was scanned at VirusTotal (Aug 14, 2020), it was detected as a malicious Java trojan by 28 of 59 antivirus applications.
Far more a short while ago, other individuals would likewise phone attention to malware that abused the security weakness, which includes this write-up in June 2020 from the Security-in-bits website.
Be’ery said the way Microsoft has dealt with the vulnerability report seems relatively odd.
“It was quite obvious to all people included, Microsoft involved, that GlueBall is indeed a legitimate vulnerability exploited in the wild,” he wrote. “Therefore, it is not apparent why it was only patched now and not two yrs back.”
Requested to comment on why it waited two years to patch a flaw that was actively being exploited to compromise the protection of Home windows pcs, Microsoft dodged the issue, indicating Home windows users who have used the newest protection updates are shielded from this attack.
“A stability update was unveiled in August,” Microsoft explained in a written statement despatched to KrebsOnSecurity. “Customers who utilize the update, or have computerized updates enabled, will be secured. We proceed to motivate shoppers to transform on computerized updates to enable guarantee they are secured.”
Update, 12:45 a.m. ET: Corrected attribution on the June 2020 weblog write-up about GlueBall exploits in the wild.
Tags: Bernardo Quintero, CVE-2020-1464, GlueBall, Peleg Hadar, SafeBreach Labs, Securityinbits.com, Tal Be’ery, Zengo

Introvert. Beer guru. Communicator. Travel fanatic. Web advocate. Certified alcohol geek. Tv buff. Subtly charming internet aficionado.